Hard disc encryption software – In today’s increasingly digital world, data security is paramount. Protecting sensitive information stored on your hard drive is crucial, and hard disk encryption software provides a robust solution. This comprehensive guide explores the intricacies of hard disk encryption, delving into various software options, their features, and considerations for choosing the right solution for your needs. We’ll also address common FAQs and security best practices.
Understanding Hard Disk Encryption
Hard disk encryption is the process of converting readable data into an unreadable format, often referred to as ciphertext. This transformation requires a cryptographic key, which acts like a password, to decrypt the data and restore it to its original form. Without the correct key, accessing the encrypted data is practically impossible, even for sophisticated attackers. This safeguards your sensitive information from unauthorized access, theft, or data breaches, whether your device is lost, stolen, or compromised.
Types of Hard Disk Encryption
Several methods exist for encrypting hard drives, each with its own strengths and weaknesses:
- Full Disk Encryption (FDE): This encrypts the entire hard drive, including the operating system, applications, and user data. It offers the highest level of protection but may slightly impact performance.
- File-Level Encryption: This encrypts individual files or folders, allowing selective encryption based on sensitivity. It’s less resource-intensive than FDE but requires careful management of which files are encrypted.
- Self-Encrypting Drives (SEDs): These drives have encryption built directly into the hardware. This offers a highly secure and transparent solution, as encryption and decryption happen automatically without requiring software installation on the host system.
Choosing the Right Hard Disk Encryption Software: Hard Disc Encryption Software
Selecting the appropriate software depends on several factors, including your operating system, security requirements, budget, and technical expertise. Consider the following aspects:
Operating System Compatibility
Ensure the software is compatible with your operating system (Windows, macOS, Linux). Some solutions offer cross-platform support, while others are specific to a particular OS. Check system requirements carefully to avoid compatibility issues.
Encryption Algorithms
The strength of encryption depends on the algorithm used. Advanced Encryption Standard (AES) with a key size of at least 256 bits is generally considered secure. Look for software that utilizes strong, well-vetted algorithms.
Key Management
Secure key management is critical. The software should provide options for strong password protection, key recovery mechanisms, and potentially hardware security modules (HSMs) for enhanced security in enterprise environments. Losing your encryption key renders your data irretrievable.
Performance Impact
While encryption adds a layer of security, it can slightly impact system performance, especially with full disk encryption. The impact varies depending on the encryption algorithm, hardware, and software implementation. Consider the trade-off between security and performance based on your needs.
User-Friendliness, Hard disc encryption software
Choose software with an intuitive interface, especially if you’re not technically proficient. Easy-to-use software minimizes the chance of errors during encryption and decryption processes. Look for clear documentation and helpful support resources.
Popular Hard Disk Encryption Software
Several reputable software options are available for various operating systems:
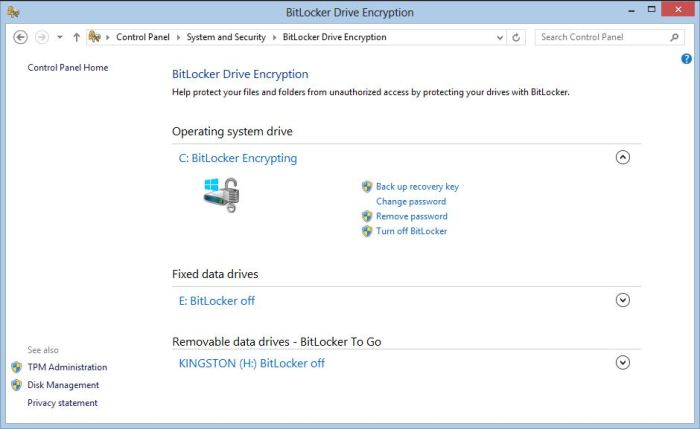
- BitLocker (Windows): Built-in full disk encryption for Windows operating systems.
- FileVault (macOS): Apple’s built-in full disk encryption for macOS.
- VeraCrypt: Open-source, free, and cross-platform software offering both full disk and file-level encryption.
- LUKS (Linux Unified Key Setup): A standard for disk encryption on Linux systems, often integrated with tools like cryptsetup.
- DiskCryptor: A free, open-source disk encryption utility for Windows.
Security Best Practices
Beyond choosing the right software, adopting secure practices is crucial:
- Use strong, unique passwords: Avoid easily guessable passwords and use a password manager to generate and store complex passwords securely.
- Enable automatic updates: Keep your encryption software up-to-date to benefit from security patches and bug fixes.
- Regularly back up your data: While encryption protects against unauthorized access, data loss can still occur due to hardware failure. Regular backups are essential.
- Secure your key: Protect your encryption key with utmost care. Losing it means losing access to your encrypted data.
- Consider multi-factor authentication (MFA): Where available, enable MFA for an extra layer of security.
Frequently Asked Questions (FAQ)
- Q: Is hard disk encryption slow? A: While encryption adds some overhead, modern algorithms and hardware are optimized to minimize performance impact. The impact can vary based on factors such as the encryption algorithm, hardware capabilities, and the amount of data being encrypted.
- Q: Can I encrypt only specific files or folders? A: Yes, file-level encryption allows you to encrypt only the data you need to protect. Full disk encryption encrypts everything on the drive.
- Q: What happens if I forget my encryption key? A: Without the correct key, your encrypted data is irretrievable. Therefore, securely storing your key is critical. Some software offers key recovery options, but this should be carefully considered.
- Q: Is hard disk encryption enough to protect my data? A: Hard disk encryption is a crucial security measure, but it’s not the only one. Combining encryption with other security practices, such as strong passwords, regular backups, and updated antivirus software, enhances overall data protection.
- Q: What is the difference between hardware and software encryption? A: Hardware encryption (like SEDs) integrates encryption directly into the hard drive, while software encryption uses software to encrypt the data on the drive. Hardware encryption is generally considered more secure as it’s less vulnerable to software attacks.
References
Conclusion
Hard disk encryption is an essential tool for protecting sensitive data. By understanding the different types of encryption, choosing the right software, and implementing secure practices, you can significantly enhance your data security posture. Don’t leave your valuable information vulnerable – invest in hard disk encryption today.
Call to Action (CTA)
Start protecting your data now! Download a reputable hard disk encryption software and secure your digital assets. Choose the solution that best fits your needs and technical expertise. Don’t wait until it’s too late – encrypt your hard drive today!
Essential FAQs
What are the different types of hard disc encryption?

Source: techviral.net
Common types include full-disk encryption (FDE) which encrypts the entire drive, and file-level encryption which encrypts individual files or folders.
Is hard disc encryption slow?
Modern encryption algorithms are highly optimized and the performance impact is often minimal, though it can vary depending on the hardware and software used.
What happens if I forget my encryption password?

Source: explorateglobal.com
Data recovery is generally impossible without the correct password. Choose a strong, memorable password and consider using a password manager.
Can I encrypt an external hard drive?
Yes, most hard disc encryption software can be used to encrypt external drives as well.
Is hard disc encryption enough to secure my data?
Source: poweradmin.com
Hard disc encryption is a crucial step, but it should be combined with other security measures like strong passwords, regular software updates, and antivirus protection for comprehensive security.
